The Importance of Encryption: Understanding the Implications of Apple’s Lawsuit with the FBI
On December 2, 2015, Syed Farook and Tashfeen Malik attacked the Inland Regional Center in San Bernardino killing 14 people and wounding 22. Farook’s iPhone was recovered from the site of the shooting. In the process of its investigation, the FBI accidentally locked the iPhone and reset its password, preventing any data on the phone from being retrieved. The FBI then turned to Apple, and requested a backdoor to be built into the operating software of the phone in order to gain access to any location data or communications on the phone, which could aid in finding any accomplices in the shooting.
While a seemingly logical step in progressing the investigation into a deadly domestic attack, building a backdoor to hack into the shooter’s iPhone would bring about a number of serious consequences, and threaten the right to privacy for every citizen in the United States.
Apple issued a letter on February 16th, 2016, stating that it would not give in to the FBI’s demands, citing security concerns and arguing that “compromising the security of our personal information can ultimately put our personal safety at risk.”
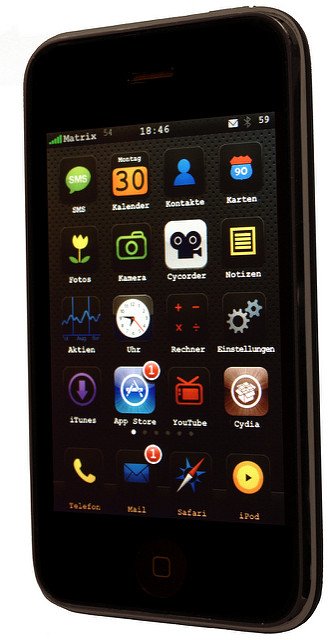
From a purely private economic standpoint, it is bad business to build a backdoor into a product. If there is a way into your operating system, private individuals will be able to take advantage of it. By giving in to the FBI’s demands, Apple would be undermining their own product, and taking away a major selling point of their hugely successful smartphone.
Looking at the big picture, the implications are much scarier. This is only the latest development in the public discourse on encryption and personal privacy. The topic was brought to the fore with the revelations of Edward Snowden regarding the NSA’s controversial PRISM program, which, according to The Guardian, “[collected] the communication records of millions of US citizens…indiscriminately and in bulk – regardless of whether they are suspected of any wrongdoing.”
Apple’s compliance, whether legally mandated or not, could be interpreted as a violation of the sixth article of the Bill of Rights, which states that “the right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated, and no Warrants shall issue, but upon probable cause, supported by Oath or affirmation, and particularly describing the place to be searched, and the persons or things to be seized.” Though messages, photos, and other files on an iPhone are not ‘papers,’ it is no stretch of the definition to consider them as such. If the legal interpretation of the sixth article sees digital files as the same as physical ones, the NSA’s data collection was a clear abuse of power, and a backdoor into Apple’s operating system is creating the potential for yet another violation.
Additionally, under the Fourteenth Amendment of the Constitution, it is stated that “No State shall make or enforce any law which shall abridge the privileges or immunities of citizens of the United States; nor shall any State deprive any person of life, liberty, or property, without due process of law.” Of course, liberty and the right to privacy are not one and the same – the right to privacy is not included explicitly in the Constitution, or in the Bill of Rights – although they could be interpreted as such in this context.
But the lack of explicit coverage by either the Constitution or the Bill of Rights leads to a multitude of possible legal interpretations to the rights of American citizens in regards to personal privacy. This also means that the precedent set by the Apple case would either be a clear victory for the right to privacy, or a step towards what Ted Olson, one of Apple’s head lawyers, described as a “big brother” type society.
This precedent is extremely important as Obama leaves office and new policies begin to be implemented. However, it is important to note that Obama defended the PRISM program, saying that “we’ve struck the right balance” in regards to what the NSA collected and what was revealed to the public. Bernie Sanders has stated that he would end the NSA’s bulk collection, while Hillary Clinton has called for greater online surveillance in the wake of the San Bernardino shootings, but at the same time has supported reforms to the NSA’s call data collection program. On the other end of the spectrum, both Marco Rubio and frontrunner Donald Trump believe that the NSA’s controversial PRISM program should be continued, with only Ted Cruz is opposing a revival of the program, arguing that “more data from millions of law abiding Americans is not always better data.”
So what does all of this mean? Apple states in their letter that “While the government may argue that its use would be limited to this case, there is no way to guarantee such control.”
The backdoor that the FBI wants Apple to create would essentially be a hacked version of the standard operating system, which would then be installed on the iPhone and would allow the passcode to be broken through brute force – which means that a computer runs through every possible password combination until one works. However, such an operating system could be installed and used to break into any iPhone, not just the one that was used in the shooting.
This is a fact that is recognized by Congress, who accused the Justice Department of “overreaching its authority and undermining both privacy and cybersecurity” by bringing this lawsuit against Apple into existence. Robert Goodlatte, a Republican congressman from Virginia, questioned FBI director James Comey, saying “It won’t be a one-time request. It’ll set precedent for other requests from the FBI and any other law enforcement,” to which Comey replied “Sure, potentially.”
Furthermore, the legal precedent that would be set by allowing the government to gain access into an iPhone would make it easier for them to gain additional backdoors into the operating systems of other smartphones, and other electronic devices that make use of similar encryption measures. Considering the NSA’s track record regarding mass surveillance, and the fact that many presidential candidates support that program, backdoors like the one the FBI requested of Apple are no stretch of the imagination. By setting such a precedent, various other government agencies could request further workarounds and backdoors, allowing for an even greater degree of data collection than what was already experienced under the NSA’s PRISM program.
Domestic security and measures to prevent mass shootings like the one in San Bernardino are important issues that politicians and officials need to take seriously. While there is no evidence to definitively link either Farook or Malik to terrorist groups, the Chattanooga shooting in July of 2015 “was inspired by a foreign terror organization,” according to Comey. To say that measures should not be taken against these sorts of attacks would not be rational, but neither would the implementation of measures that would strip the privacy of individuals who have done nothing wrong, and open the window for further government abuse of power when it came to digital surveillance. A balance must be struck, but not the balance of Obama and the NSA. It should be a balance where individuals who wish to inflict harm on others have a harder time accessing weapons, and where the private information of citizens is not collected without probable cause.
